Cyber Security
Phone: 262-522-8560
Ontech Systems, Inc.
11800 W Park Place
Milwaukee, WI 53224 Hours: M-F 8am – 5pm
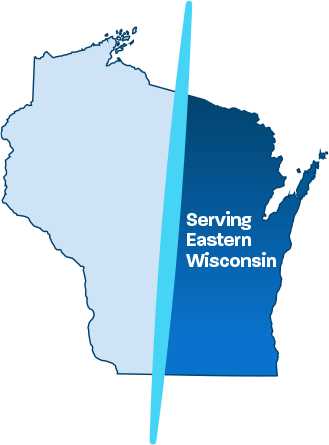
Areas We Serve
Milwaukee, Waukesha, Wauwatosa, Mequon, Menomonee Falls, Brown Deer, Hartford, Brookfield, West Bend, Germantown, Oshkosh, Appleton, Neenah, Green Bay, Sheboygan, Fond Du Lac
© 2026 Ontech Systems, Inc.







