ARE STRONG PASSWORDS WORTH THE EXTRA EFFORT?
7 Password Do’s and Don’ts
Cybersecurity is a growing concern for businesses of all sizes and it’s no wonder – cybercrime is big business.
The Worst Password Mistakes and How to Fix Them
Follow these do’s and don’ts and avoid putting yourself (and your company) at risk.
And while it’s human nature to take shortcuts, if you’ve ever been on the receiving end of a cyber-attack, you know a strong password is worth the effort.
Most people have basic knowledge about cyber security, but it’s very likely that your definition of a strong password and an IT professional’s definition – are entirely different.
Password DO’s
1. Create strong passwords.
You might think you are being clever by combining your best friend’s first name, your first pet and the street you grew up on as your password, and while that might help you remember your password, it’s not strong enough.
It’s best to use characters, numbers and symbols to create a strong password.
TIP: Start with a phrase you can remember. “I want to go to Italy”. Now convert that to a password using the first letter in each word and change the word “to” into the number “2”: iw2g2i! and add an exclamation point at the end.
Finally, add a capital first and last letter of the website you are on using your new password.
For example, if you need a Facebook password, this password would turn into Fiw2g2i!K. This method gives you a strong password that is entirely unique to you!
2. Change your passwords regularly.
While this is a best practice for all websites, it’s especially important for email accounts, online banking and any other website that contains highly sensitive information. It is recommended (at minimum) to change your passwords every 3 months.
3. Keep your passwords safe.
If you use the password generation method above, you’ll always be able to remember your password for various websites, but there are various password managers that can make remembering your password effortless such as Last Pass, RoboForm, and Kaspersky Password Manager.
4. Enable 2-Step Verification.
Otherwise known as multi-factor authentication, this extra security precaution is often seen on online banking and even Gmail accounts. 2-step verification is becoming more prevalent on popular websites like Facebook as well. Multi-factor authentication links your username and password with a backup email or phone number – or in some cases, a fingerprint. This ensures you, and you alone have access to your account.
Password DON’Ts:
5. Don’t use the same password on every website.
At Ontech Systems, we are continually surprised by the number of people that use the same password on every website. As it is, more often than not, these passwords are not very secure, but to make matters worse, these weak passwords are used across many different websites!
According to TeleSign, on average, people use only 6 unique passwords to protect 24 separate online accounts. Don’t make this mistake.
6. Don’t allow your browser to save your password.
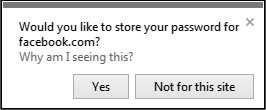 Just as you would not want your browser to save all your payment details, it’s best to prevent prying eyes from viewing your passwords on your PC or mobile device.
Just as you would not want your browser to save all your payment details, it’s best to prevent prying eyes from viewing your passwords on your PC or mobile device.
Did you know…
In Firefox, if you don’t enable a master password, anyone who has physical access to your computer can view your saved passwords by clicking options > show passwords? It’s best practice to avoid using browser saved passwords completely. Use a secure password manager instead – it’s as easy as that!
7. Don’t use personal information when creating a password.
It’s actually quite common for people to use their birthday when creating a password.
What’s even more prevalent, is the use of common words. Hackers have dictionary-based tools they use to crack these types of passwords, so be sure to follow the first “do” tip in this article and make your passwords as random and meaningless as possible.